Count Down
Wonderful not to be missed
- 52D
- 22Hr
- 08Min
- 24Sec
ISC
ISC (Internet Security Conference) is an international cyber security conference, jointly sponsored by China Cyber Security Association and 360 Cyber Security Center under the guidance of the cyberspace administration of China, the ministry of industry and information technology, and the ministry of public security.
It has far-reaching influence in Asian-Pacific Region.
Founded in 2013, ISC has been held for 7 terms until now, with 14 international summits, more than 100 parallel sessions, and over 20 featured activities developed. About 200 foreign experts from more than 30 countries throughout the world have participated in ISC, with more than 1,000 speech topics involved; it has been reported by about 1,000 media, and accumulatively received more than 200,000 person-time visitors.
Following the concept of openness, ISC aims to promote more cooperation with government, security enterprises home and abroad, colleges and universities, and research institutions. Nowadays, ISC has already become a world leading internet security technology platform. It leads the trend of global internet security development.
ISC (Internet Security Conference) is an international cyber security conference, jointly sponsored by China Cyber Security Association and 360 Cyber Security Center under the guidance of the cyberspace administration of China, the ministry of industry and information technology, and the ministry of public security.
It has far-reaching influence in Asian-Pacific Region.
Founded in 2013, ISC has been held for 7 terms until now, with 14 international summits, more than 100 parallel sessions, and over 20 featured activities developed. About 200 foreign experts from more than 30 countries throughout the world have participated in ISC, with more than 1,000 speech topics involved; it has been reported by about 1,000 media, and accumulatively received more than 200,000 person-time visitors.
Following the concept of openness, ISC aims to promote more cooperation with government, security enterprises home and abroad, colleges and universities, and research institutions. Nowadays, ISC has already become a world leading internet security technology platform. It leads the trend of global internet security development.
Guests Review
-

Wu Hequan
Honorary Chairman of ISC 2019
Academician of Chinese Academy of Engineering
-

Zhou Hongyi
Chairman of ISC
Chairman and CEO of the 360 Group
-
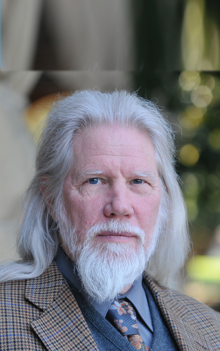
Whitfield Diffie
Winner of the 2015 Turing Prize
-

Thomas J.Sargent
Winner of the 2011 Nobel Memorial Prize in Economic Sciences
-

Avi Dichter
Current Chairman of the Foreign Affairs and Defense Committee
-

Anatoly Smienov
General Director, National Association of International Information Security, Russia
-
August 19
-
August 20
Main Forum
-
9:30-9:55
Opening Speech
-
9:55-11:25
Insight and Cyber Warfare
Israel and Cyber Security—Avi Dichter
Application and Development of Cybersecurity Technology in a Challenging Context—Whitfield Diffie
Collaboration and Cooperation toward a Safe and Secure Cyberspace—David Koh
Thoughts on the Construction of Israel's National Defense System for Cyberspace Security—Erez Kreiner
Cybersecurity Economics: Costs and International Aspects—Tomas J. Sargent
Actual Problems of International Information Security - a View from Russia—Anatoly Smirnov
-
11:25-11:55
Thinking and Cyber Warfare
Challenges and Responses in the Cyber Warfare Era—Zhou Hongyi
-
13:30-13:45
Opportunities and Cyber Warfare
Big Challenge, Broad Security and Great Opportunities - Outlook of IT Security Market in China and the World—Wu Lianfeng
-
13:45-16:35
Action and Cyber Warfare
Overview of the Latest Windows OS Kernel Exploits Found in the Wild—Alexander Liskin/Boris Larin
Years of tracking NSA Cyber Weapons—Zheng Wenbin
Selling 0-Days to Governments and Offensive Security Companies—Maor Shwartz
Introducing the Innovative Mechanism of Israel's Network Security Industry—Oren Elimelech
Security Challenges and Practices in the Era of Digital Economy—Frank Fan
Core of Bigdata Security - Independence of Third-party Security—Ouyang Meiwen
New Challenges, New Architecture, New Responses—Yang Bin
-
19:00-21:00
Banquet
-
Security Forum for Domestic-made Computing Platform Terminals
-
5G Security Forum
-
Critical Infrastructure Security Forum
-
Urban Security Forum
-
Security Big Data
-
Industrial Internet Security Forum
-
Forum of the Theory and Practice of Digital Forensics
-
Forum of Personal Information Security and Privacy Protection
-
Artificial Intelligence (AI) and Security Forum
-
Forum of Vulnerability Research and Exploitation
-
CS·2019: Enterprise Cybersecurity Solutions Forum
-
Network Monitoring and Response Forum
-
Cybersecurity Talent Training Forum
-
CLOSED-DOOR MEETING
Focus on Industry Hotspots
The Most Influential Network Security Event in the World
Highlights preempt
-
Seven years'inheritance of trade unions
Sublimation of Purpose and Purpose
-
Seven years'inheritance of trade unions
Sublimation of Purpose and Purpose
-
Seven years'inheritance of trade unions
Sublimation of Purpose and Purpose
-
Seven years'inheritance of trade unions
Sublimation of Purpose and Purpose
Conference venue



